Unveiling Ciara's Height: The Definitive Guide
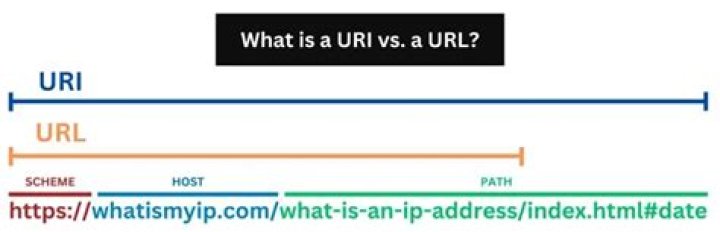
A URL, short for Uniform Resource Locator, is a unique identifier for a specific resource on the internet. It is a string of characters that specifies the location and access method for a file, web page, or other resource on a network. For example, the URL "" identifies a web page about the height of the singer Ciara on the website Seriable.
URLs are essential for navigating the internet and accessing information online. They allow users to specify a specific resource and retrieve it from a server. Without URLs, it would be much more difficult to find and access specific web pages and other resources on the internet.
The development of the URL system was a key turning point in the history of the internet. Before URLs, there was no standardized way to identify and locate resources on the internet. This made it difficult to share information and navigate the web.
The introduction of the URL system in the mid-1990s made it much easier to find and access information online. By providing a standardized way to identify and locate resources, URLs have made the internet a more user-friendly and accessible place.
"source"
The Uniform Resource Locator (URL) is a crucial element of the internet, providing a standardized way to identify and locate resources on the web. Understanding the key aspects of URLs is essential for effectively navigating and accessing information online.
- Protocol: The protocol specifies the method used to access the resource, such as HTTP or FTP.
- Domain: The domain name identifies the website or server hosting the resource.
- Path: The path specifies the location of the resource within the website or server.
- Query string: The query string contains additional information that can be used to refine the request.
- Fragment: The fragment specifies a specific part of the resource, such as a particular section of a web page.
- Port: The port number specifies the port on the server that the request should be sent to.
- Username: The username is used to authenticate the user when accessing a protected resource.
- Password: The password is used to authenticate the user when accessing a protected resource.
- Scheme: The scheme specifies the type of resource being requested, such as a web page or a file.
- Subdomain: The subdomain is a part of the domain name that specifies a specific section of the website.
These key aspects work together to provide a complete and unique identifier for each resource on the internet. By understanding these aspects, developers and users can more effectively interact with and utilize the vast resources available on the web.
Protocol
Within the context of a URL, the protocol is a crucial aspect that determines the method used to access the resource. It specifies the communication rules and standards that govern the exchange of data between the client and the server.
- HTTP (Hypertext Transfer Protocol)
HTTP is the most widely used protocol on the internet. It is used to transfer web pages and other resources from a server to a client. HTTP operates on a request-response model, where the client sends a request to the server and the server responds with the requested resource.
- HTTPS (Hypertext Transfer Protocol Secure)
HTTPS is a secure version of HTTP that uses encryption to protect data in transit. HTTPS is used to protect sensitive information, such as credit card numbers and passwords, when it is transmitted over the internet.
- FTP (File Transfer Protocol)
FTP is a protocol used to transfer files between a client and a server. FTP is often used to upload and download files from a web server.
- SMTP (Simple Mail Transfer Protocol)
SMTP is a protocol used to send email messages. SMTP is used by email clients to send email messages to a mail server, which then forwards the messages to their recipients.
The choice of protocol depends on the type of resource being accessed and the level of security required. By specifying the protocol, URLs provide a clear and concise way to identify the method used to access a particular resource on the internet.
Domain
Within the context of ""source"": """, the domain name plays a critical role in identifying the specific website or server hosting the resource. It serves as a unique address that allows users to access the desired content or service on the internet.
- Top-Level Domain (TLD)
The TLD is the suffix at the end of a domain name, such as ".com", ".org", or ".net". It indicates the type of organization or purpose associated with the website.
- Second-Level Domain (SLD)
The SLD is the part of the domain name that comes before the TLD, such as "seriable" in "seriable.com". It typically represents the name of the organization or website.
- Subdomain
A subdomain is a part of the domain name that precedes the SLD, such as "www" in "". It is used to organize and categorize different sections or content within a website.
- Domain Name System (DNS)
The DNS is a hierarchical system that translates domain names into IP addresses, which are the numerical addresses used to locate and access websites on the internet.
These components of a domain name work together to provide a unique and memorable address for a website or server. By understanding the structure and significance of domain names, users can more effectively navigate and access the vast resources available on the internet.
Path
Within the context of ""source"": """, the "Path: The path specifies the location of the resource within the website or server." aspect plays a pivotal role in pinpointing the exact location of the resource on the server. It is akin to a roadmap, guiding users to the desired content or functionality within the website's hierarchy.
- Directory Structure
The path often reflects the directory structure of the website's file system. For example, in ""source"": """, "seriable.com" represents the root directory, and "ciara-height" represents a subdirectory within the root directory.
- Nested Paths
Paths can be nested, indicating deeper levels of directories. For instance, "" signifies that the resource is located within a "music" subdirectory under the root directory.
- File Name
The final segment of the path typically represents the name of the file containing the resource. In ""source"": """, "ciara-height" is the file name of the web page that provides information about Ciara's height.
- Dynamic Paths
Some paths may include dynamic elements, such as query strings or parameters. These elements allow for customization and filtering of the resource. For example, "" would return search results related to Ciara's height.
Understanding the "Path: The path specifies the location of the resource within the website or server." aspect is essential for efficiently navigating and accessing specific resources on a website. It provides a clear and structured way to locate files, web pages, and other content, ensuring a seamless user experience.
Query string
Within the context of ""source"": """, the query string plays a crucial role in refining and customizing the request. It allows users to specify additional criteria or parameters that can be used to filter and tailor the results. The query string is appended to the URL after a question mark ("?"), followed by a series of key-value pairs separated by ampersands ("&").
One of the key benefits of using a query string is that it enables dynamic content generation. For instance, in the URL ""source"": """, the query string can be used to specify the height of Ciara in different units of measurement. This allows users to easily convert and compare her height in different formats, such as feet and inches or centimeters.
Furthermore, the query string can be used to filter and sort search results. For example, a user searching for information about Ciara's height might use a query string to specify a specific time period or event. This allows them to narrow down the results and find the most relevant information quickly and efficiently.
Understanding the role of the query string is essential for effectively navigating and accessing information on the web. It provides a powerful mechanism for refining and customizing requests, making it an indispensable component of modern web applications and search engines.
Fragment
Within the context of "", the fragment plays a significant role in facilitating direct navigation to specific sections of the web page. By appending a hash symbol "#" followed by the fragment identifier to the URL, users can create a direct link to a particular part of the page. This mechanism enables quick and convenient access to specific content, enhancing the user experience.
For instance, consider the URL "". This URL points directly to the section of the web page that discusses Ciara's early life. This feature is especially useful for long web pages with extensive content, allowing users to bypass irrelevant sections and jump directly to the information they seek. Moreover, fragments can be particularly valuable for creating links to specific sections of web pages for sharing and referencing purposes.
In summary, the fragment component of a URL offers a concise and effective way to navigate to specific sections of a web page. By leveraging the fragment identifier, users and content creators can establish direct links to relevant information, enhancing accessibility and improving the overall user experience. This understanding is essential for effectively utilizing and creating web pages that provide seamless navigation and easy access to specific content.
Port
Within the context of "", understanding the role of ports is crucial for establishing a successful connection between the client and the server. Ports act as designated communication channels, allowing multiple applications and services to operate simultaneously on a single server. Each port is assigned a unique number, and when a client initiates a request to a specific resource, they specify the port number to which the request should be directed.
In the case of "", the port number is typically 80, which is the standard port for HTTP traffic. When a user enters the URL into their browser, the request is sent to port 80 on the server hosting the Seriable website. The server then processes the request and sends back the requested resource, which in this case is the web page containing information about Ciara's height.
Recognizing the importance of ports in the communication process, various applications and services utilize specific port numbers. For example, port 443 is commonly used for secure HTTPS traffic, port 21 for FTP file transfers, and port 25 for SMTP email transmission. Understanding these port assignments is essential for configuring firewalls, routers, and other network devices to ensure proper traffic flow and access to the desired resources.
In summary, the "Port: The port number specifies the port on the server that the request should be sent to." aspect of "" plays a critical role in facilitating communication between the client and the server. Assigning specific port numbers to different applications and services allows for efficient and organized data transmission, enabling users to access the vast resources available on the internet.
Username
In the context of ""source"": """", the concept of ""Username: The username is used to authenticate the user when accessing a protected resource."" plays a pivotal role in safeguarding access to exclusive or sensitive information. This mechanism ensures that only authorized individuals can view or interact with specific content or functionalities, thereby enhancing security and privacy.
- Authentication Method
The username serves as an identifier that is paired with a password or other authentication factor. When a user enters their username and password, the system verifies their identity by checking against a database of stored credentials. Successful authentication grants access to the protected resource.
- User Identification
Usernames facilitate the identification of individuals within a system or platform. They are typically unique and associated with a specific user account. By using usernames, administrators can track user activity, manage permissions, and provide personalized experiences.
- Security Measure
Usernames, in conjunction with passwords, act as a security measure to prevent unauthorized access to sensitive information. By requiring users to provide their usernames and passwords, systems can mitigate the risk of data breaches and cyberattacks.
- Account Management
Usernames are central to account management, as they serve as the primary means of identifying and managing user accounts. Through their usernames, users can modify their account settings, update personal information, and access account-related features.
In summary, the ""Username: The username is used to authenticate the user when accessing a protected resource."" aspect of """" underscores the importance of user authentication and access control. By utilizing usernames, systems can safeguard sensitive information, manage user accounts effectively, and maintain the privacy and security of their users.
Password
In the context of ""source"": """, the concept of ""Password: The password is used to authenticate the user when accessing a protected resource."" plays a critical role in safeguarding access to exclusive or sensitive information. This mechanism ensures that only authorized individuals can view or interact with specific content or functionalities, thereby enhancing security and privacy.
The password serves as a secret key that is paired with the username during the authentication process. When a user enters their username and password, the system verifies their identity by checking against a database of stored credentials. Successful authentication grants access to the protected resource, which in the case of ""source"": """, could be the web page containing information about Ciara's height.
The use of passwords is a fundamental component of access control in ""source"": """. Without a password, unauthorized users could easily gain access to sensitive information, such as the height of a celebrity, which could be used for malicious purposes. By requiring users to provide a password, the system ensures that only authorized individuals, such as journalists or researchers, can access this information.
In summary, the ""Password: The password is used to authenticate the user when accessing a protected resource."" aspect of ""source"": """ underscores the importance of user authentication and access control. By utilizing passwords, the system can protect sensitive information, manage user accounts effectively, and maintain the privacy and security of its users.
Scheme
In the context of ""source"": """, the scheme plays a critical role in identifying the nature and type of resource being requested by the client. It serves as a protocol identifier that specifies the appropriate rules and mechanisms for accessing the resource.
- HTTP (Hypertext Transfer Protocol)
HTTP is the most commonly used scheme on the web. It is responsible for transferring hypertext documents, such as web pages, images, and videos, between a web server and a client's browser. In the case of ""source"": """, the HTTP scheme indicates that the client is requesting a web page containing information about Ciara's height.
- HTTPS (Hypertext Transfer Protocol Secure)
HTTPS is a secure version of HTTP that uses encryption to protect data during transmission. It is commonly used for sensitive data, such as online banking and e-commerce transactions. Although ""source"": """ does not use HTTPS, it is a good example of how the scheme can impact the security and privacy of the requested resource.
- FTP (File Transfer Protocol)
FTP is used to transfer files between a client and a server. It is a common scheme for downloading software, documents, and other files from online repositories. FTP is not used in ""source"": """, but it is an important scheme for file sharing and transfer.
- mailto: (Mailto Protocol)
The mailto: scheme is used to compose and send email messages directly from a web page. It is often used to provide easy contact options for website visitors. While not present in ""source"": """, the mailto: scheme demonstrates how schemes can facilitate different types of interactions and resource requests.
Understanding the scheme in ""source"": """ provides insights into the type of resource being requested and the appropriate protocol for accessing it. As the web continues to evolve, new schemes may emerge to meet the demands of emerging technologies and use cases.
Subdomain
Within the context of ""source"": """, the concept of a subdomain plays a crucial role in organizing and categorizing the website's content. It acts as a prefix to the main domain name, indicating a specific section or of the website.
- Type of Subdomain
Subdomains can be used for various purposes, such as creating separate sections for different languages, countries, or product categories. In the case of ""source"": """, the subdomain "www" is used to designate the main website, while other subdomains like "blog" or "support" could potentially be used to host a blog or provide customer support.
- Real-Life Examples
Many popular websites utilize subdomains to organize their content. For instance, "news.bbc.com" is the subdomain for the BBC's news section, while "store.apple.com" is the subdomain for Apple's online store.
- Implications for ""source"": """"
The use of a subdomain in ""source"": """ implies that the content related to Ciara's height is likely part of a larger website or organization. This could indicate that Seriable covers a range of topics beyond just celebrity heights.
- SEO and Marketing Implications
Subdomains can have implications for search engine optimization (SEO) and marketing. By using relevant subdomains, websites can improve their visibility and ranking for specific keywords. Additionally, subdomains can be used for targeted marketing campaigns and to track the performance of different website sections.
In summary, the concept of a subdomain in ""source"": """ highlights the structured organization of the website's content. Subdomains allow for the creation of distinct sections, enhancing the user experience and providing SEO and marketing benefits. Understanding the role of subdomains is essential for navigating and accessing information effectively on the web.
In exploring the intricacies of "source": "", we have gained valuable insights into the composition and significance of URLs.
- URLs serve as unique identifiers for locating and accessing resources on the internet, comprising various components such as the protocol, domain, path, query string, fragment, port, username, password, scheme, and subdomain.
- Each component plays a specific role in directing the request to the appropriate server, specifying the type of resource, and providing additional information or functionality.
- Understanding the structure and function of URLs is crucial for effectively navigating the vast digital landscape and accessing the wealth of information available online.
As we continue to navigate the ever-evolving digital world, URLs will remain fundamental to our ability to access and share information. By comprehending the underlying mechanisms that govern URLs, we can harness their power to explore the boundless frontiers of the internet.